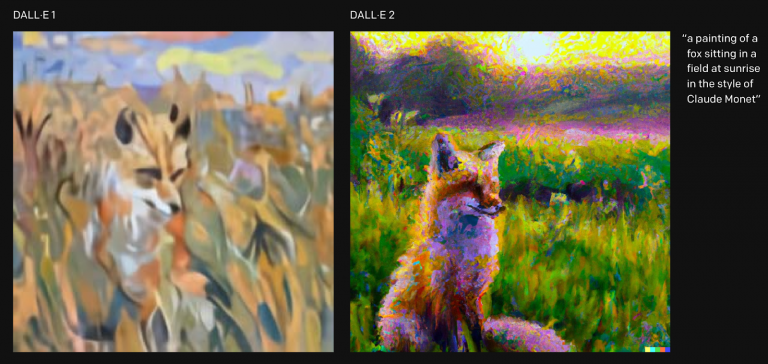
DALL.E 2: To infinity and beyond sentence-to-image generations.
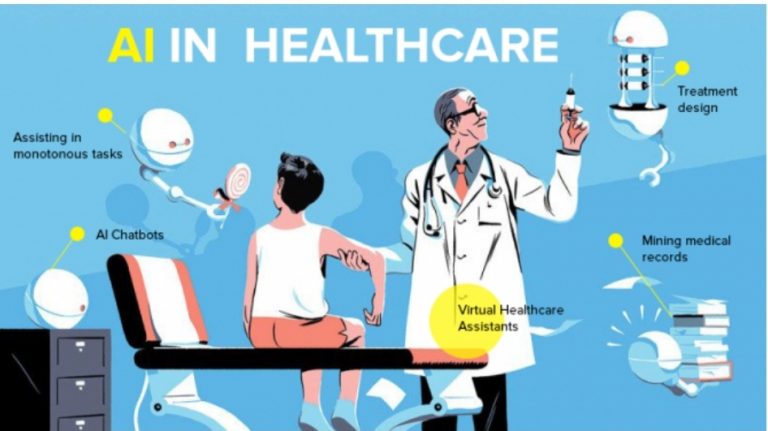
Since the dawn of the computers humans have theorized about a kind of human like intelligence developed form a computer who would dominate the human race, well that was the theory in practice artificial intelligence is a simulation of human intelligence by machines done with the help of vast amount of data which is used to get a desired outcome.